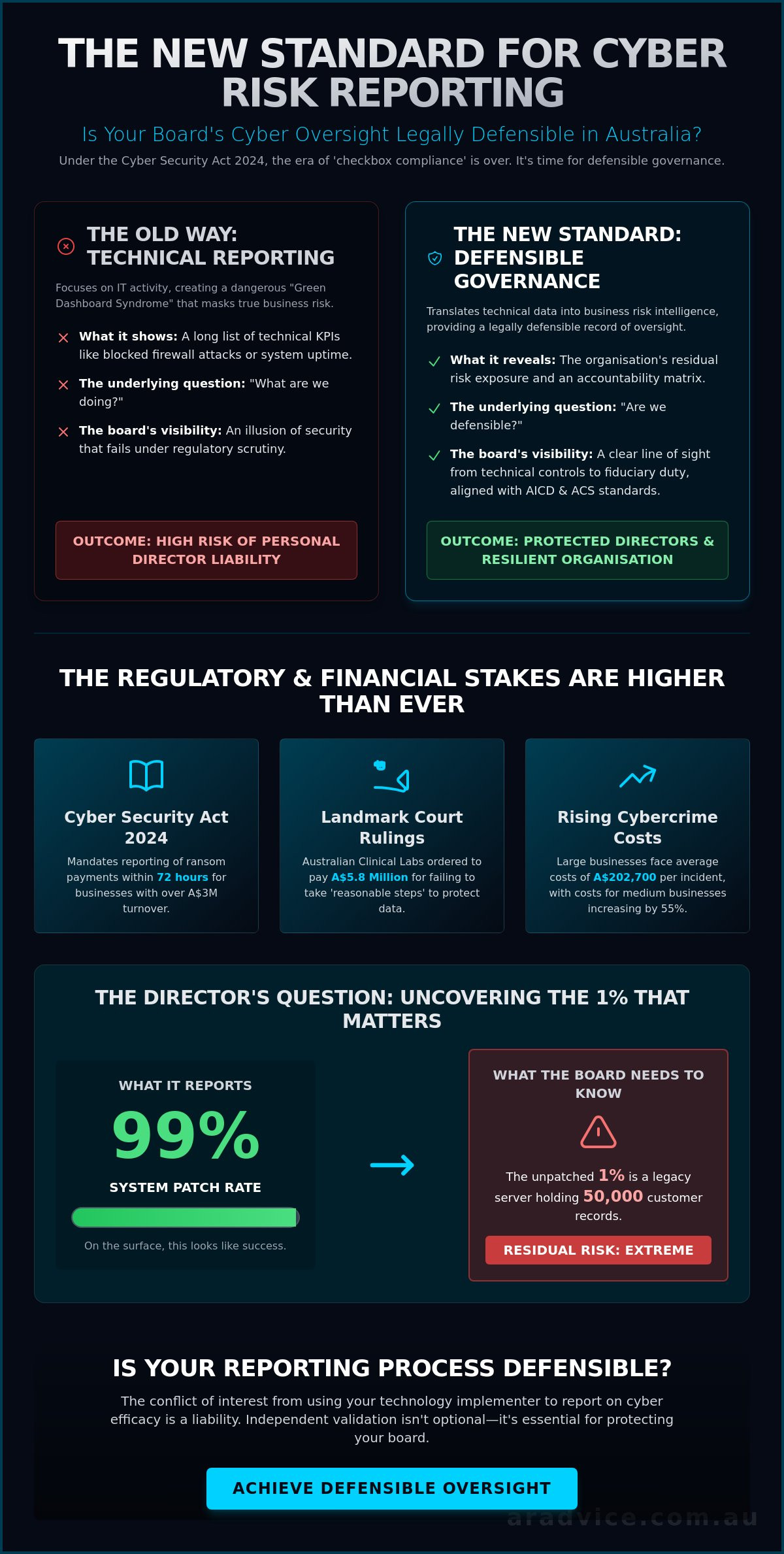
Could your board defend its cyber oversight in a court of law tomorrow? In October 2025, Australian Clinical Labs was ordered to pay a A$5.8 million penalty for failing to take reasonable steps to protect data; a landmark ruling that shifted the focus from IT departments to director accountability. As the Cyber Incident Review Board begins its work under the Cyber Security Act 2024, the era of checkbox compliance is over. Effective cyber risk reporting to the board Australia must now go beyond technical KPIs to establish a record of informed, defensible governance.
You likely feel the pressure of drowning in technical data that fails to clarify your actual risk exposure or fiduciary liability. We understand that a list of blocked firewalls doesn't satisfy your duty under APRA CPS 234. This article will show you how to translate raw technical metrics into board-ready intelligence that aligns with AICD and ACS standards. We'll preview a reporting framework that transforms abstract bits and bytes into concrete business risk, ensuring your oversight stands up to the most rigorous regulatory audit.
Key Takeaways
- Learn to translate technical vulnerabilities into the language of fiduciary duty to meet the heightened expectations of the Cyber Security Act 2024.
- Understand the inherent conflict in traditional technology consulting and why independent validation is critical for objective board visibility.
- Implement a structured framework for cyber risk reporting to the board Australia that focuses on strategic risk and defensible readiness rather than just checkbox compliance.
- Discover how the "What IT Reports vs. What We Reveal" diagnostic identifies the critical information gaps that often lead to personal director liability.
The New Standard for Cyber Risk Reporting to the Board in Australia
By 2026, the benchmark for governance has moved decisively beyond the IT department. Board-level reporting is no longer a technical summary; it's the translation of vulnerabilities into fiduciary risk assessments. Effective cyber risk reporting to the board Australia ensures directors aren't just informed, but protected. This shift is explored deeply in our guide on Cyber Governance for Boards Australia, which highlights why technical metrics alone fail to provide defensible oversight. In a landscape where the average large business faces cybercrime costs of A$202,700, the board's role is to ensure these figures don't escalate into existential threats.
The Cyber Security Act 2024, which came into full effect on 1 May 2026, fundamentally altered reporting obligations for critical infrastructure. It mandates reporting ransom payments within 72 hours for businesses with over A$3 million turnover. This legislation moves the needle from "checkbox compliance" to "defensible oversight." If your reporting doesn't reflect these legal realities, you're operating in a governance vacuum. Directors now need a clear view of how their organisation meets the "reasonable steps" benchmark set by recent court rulings.
Regulatory Scrutiny and the Cyber Incident Review Board
The newly established Cyber Incident Review Board conducts no-fault reviews of significant Australian incidents. These reviews don't just look at code; they look at the board's paper trail. Your historical reporting records become primary evidence during post-incident scrutiny. Directors must ensure their reporting aligns with AICD and ACS professional standards to prove they've exercised due diligence. This is about building a contemporary IT risk management framework that supports strategic decision-making rather than just technical maintenance.
Translating Technical Jargon into Governance Intelligence
Consider the "Director’s Question." Management might report a 99% patch rate. On the surface, this looks like success. However, if the unpatched 1% resides on a legacy server containing 50,000 customer records, the governance risk remains extreme. Reporting must pivot from "What happened?" to "What is our residual risk exposure?" Boards need to see the accountability matrix, not just the firewall logs. For those seeking structured oversight models, our Information for Directors provides a clear path to bridging the gap between the server room and the boardroom.
Why Traditional Technology Consulting Services Often Fail the Boardroom
Traditional technology consulting often creates a dangerous feedback loop. When the firm responsible for implementing security controls is also tasked with reporting on their efficacy, objectivity is compromised. This inherent conflict of interest leaves boards with a "clean" bill of health that may not survive regulatory scrutiny. For directors, cyber risk reporting to the board Australia must be an independent verification of management’s claims, not a self-graded homework assignment from a technical vendor. Implementation-focused metrics tell you if a tool is working; governance-focused reviews tell you if the organisation is resilient.
A technical vendor might report that 100% of laptops are encrypted. An independent advisor will ask if the board has the authority and process to manage the fallout when a device belonging to a high-risk executive is stolen. The difference is the gap between technical activity and fiduciary duty. In February 2026, FIIG Securities was ordered to pay a A$2.5 million penalty for cybersecurity failings under its AFSL. This underscores that regulators don't care if your IT project was completed on time; they care if your oversight was robust enough to prevent systemic failure.
The Gap Between IT Implementation and Strategic Oversight
Technical teams often suffer from "Green Dashboard Syndrome." They present KPIs that show activity, such as the number of blocked attacks or system uptime. These metrics are often irrelevant to fiduciary duty. Directors need to know how the 55% increase in cybercrime costs for medium-sized businesses impacts their specific risk profile. You need a bridge between the CISO’s technical view and your fiduciary responsibility. Reporting must move from "What are we doing?" to "Are we defensible?"
Selecting Independent Advisors for Defensible Reporting
In the event of a significant incident, the Cyber Incident Review Board will examine the quality of your oversight. Relying on implementers for risk validation is a governance failure. Directors should seek advisors who operate on a fixed-fee basis and have no interest in software or hardware sales. This ensures the intelligence you receive is unbiased and strictly aligned with AICD and ACS guidelines. To secure an objective baseline, you might consider a Cyber Governance Readiness Review to identify the gaps your current vendors may be missing.
Implementing a Defensible Framework for Board-Ready Cyber Intelligence
Establishing a robust record of governance requires a structured approach to information flow. Effective cyber risk reporting to the board Australia should be organised into a three-tier framework: Strategic Risk, Regulatory Compliance, and Incident Readiness. This structure ensures that directors aren't just looking at technical uptime, but are instead evaluating how cyber threats impact the organisation's long-term viability and its obligations under the Cyber Security Act 2024. By categorising data this way, the board can move from passive recipients of IT updates to active participants in risk management.
To identify hidden vulnerabilities, we employ the "What IT Reports vs. What We Reveal" diagnostic. While management might report that all systems meet the ASD Essential Eight maturity level two, our independent review might reveal that the escalation protocols for a breach in a subsidiary are undefined. This gap is where personal liability often resides. Testing these reporting lines through facilitated incident simulations is the only way to ensure the board receives the right intelligence under the high-pressure conditions of a real-world attack.
The 48-Hour Governance Readiness Review
Boards often lack the luxury of long-term consulting engagements when regulatory deadlines loom. Our high-impact model identifies reporting blind spots within 48 hours, providing an independent verification of management claims that is free from vendor bias. This review provides the intellectual rigour needed to satisfy the Cyber Incident Review Board that you've exercised proper diligence. Defensible oversight is a documented process of informed decision-making. It's the final step in ensuring your board's actions are beyond reproach in the event of a regulatory audit.
Actionable Steps for the Next Board Meeting
Directors should immediately standardise the cyber agenda item to focus on risk appetite and specific escalation triggers. Stop accepting dense technical logs; instead, request a plain English summary of residual risk following any major system updates or legislative changes. This ensures the board remains focused on strategic outcomes rather than technical implementation. For smaller organisations or private firms, our Founder and Sole Director Advisory provides the same level of sophisticated oversight tailored to more streamlined board structures. Start by asking management to define the exact A$ value of a 24-hour total system outage.
Securing Your Board's Defensible Position for 2026
The landscape of 2026 leaves no room for ambiguity. Directors can't rely on technical dashboards to satisfy their fiduciary duties. You've seen how the Cyber Security Act 2024 and the Cyber Incident Review Board have raised the bar for accountability. Effective cyber risk reporting to the board Australia requires an independent lens that strips away vendor bias and focuses on strategic resilience. It's about ensuring your oversight stands up to the scrutiny of a post-incident audit.
By moving beyond technical metrics, you establish a documented record of informed decision-making that protects both the organisation and your personal liability. Our specialist advisory provides a bridge between technical teams and the boardroom. We operate with no conflicts of interest; this ensures our insights align strictly with AICD and ACS professional standards. Establish your board’s defensible oversight with an independent Cyber Governance Readiness Review. You have the tools to turn cyber risk from a technical hurdle into a core governance strength.
Frequently Asked Questions
What are the legal requirements for cyber risk reporting to the board in Australia?
Directors must meet oversight obligations defined by the Corporations Act 2001 and specific standards like APRA CPS 234. The Cyber Security Act 2024 now mandates that businesses with over A$3 million turnover report ransom payments within 72 hours. Reporting isn't a suggestion; it's a legal trigger. To establish a defensible record, your reports must prove the board took "reasonable steps" to manage risk as defined by the AICD and ACS professional standards.
How often should an Australian board receive a cyber risk report?
The Australian Signals Directorate recommends cyber security as a standing agenda item for every board meeting. While quarterly deep dives are standard, the 50% rise in cybercrime costs seen in 2024-25 suggests monthly updates are more appropriate for high-risk sectors. Critical infrastructure entities require established escalation protocols that ensure significant incidents are reported to the board immediately to meet the 72-hour federal reporting window.
What is the difference between a technical cyber dashboard and a governance report?
Technical dashboards track operational activity like patch rates or blocked malware pings. Governance reports translate these metrics into business impact and residual risk. Effective cyber risk reporting to the board Australia focuses on the accountability matrix and fiduciary duty rather than system uptime. A dashboard tells you the locks are on the doors; a governance report tells you if the insurance policy is valid and who's responsible if the keys are stolen.
Can Australian directors be held personally liable for inadequate cyber reporting?
Yes, directors face personal liability under Section 180 of the Corporations Act for failing to exercise due diligence in cyber oversight. Recent penalties, such as the A$2.5 million fine against FIIG Securities in February 2026, demonstrate that regulators are targeting governance failures. Your reporting history is the primary evidence used in court to determine if you met your duty of care. Inadequate reporting isn't just an IT issue; it's a direct threat to your professional standing.








